Technical Training
Train with our team and experience next level engagement
Train with professionals who speak from their actual experience in the technology industry.
Our offerings include the below:
Ethical Hacking
Artificial Intelligence Literacy
Cyber Defense
IT Engineering



WOrkshops
AI Literacy: UNDERSTAND, USE & THRIVE IN THE AGE OF AI
Gain a strong foundation in artificial intelligence with this hands-on AI Literacy course designed for beginners of all backgrounds. Whether you’re new to AI or already exploring tools like ChatGPT, this session will help you understand how AI works, how to use it effectively, and how to think critically in a world powered by intelligent systems.
Understand the fundamentals of AI in a simple, clear way
Learn how to prompt AI tools effectively and get better results
Explore real-world use cases, ethics, and safety in AI
Build critical thinking, creativity, and future-ready skills
CODE Red Team: Learn the Art of Ethical Hacking
Master the fundamentals of penetration testing and offensive security in this hands-on workshop led by industry experts. Learn the core skills needed to think like an attacker and strengthen cybersecurity defenses for an organization
Linux fundamentals for ethical hacking
Reconnaissance techniques & intelligence gathering
Network attacks & exploitation methods
Web application security testing
AWS Networking: Build & Connect in the Cloud
Gain a solid foundation in cloud networking with this hands-on AWS Networking Workshop. Whether you’re a beginner or a tech professional, this session will help you understand key networking concepts and how they apply to cloud computing.
Learn the fundamentals of cloud networking
Build and configure a network in AWS
Live demo with Q&A session
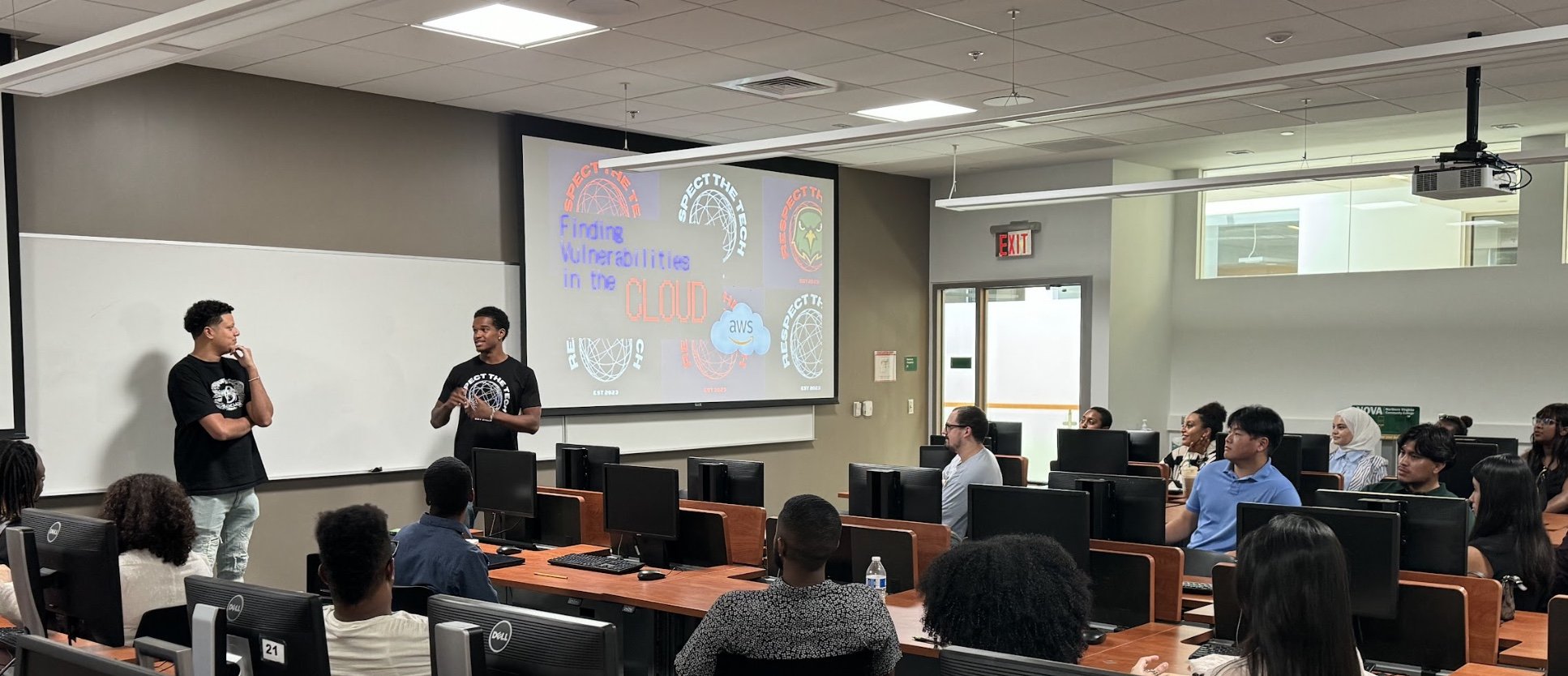
Vulnerability Analysis:
Learn how to identify, assess, and remediate vulnerabilities in real-world environments. In this hands-on workshop, you'll build and configure a virtual machine in AWS, scan for weaknesses using Nessus Essentials, and analyze the results to develop effective remediation strategies.
Understand vulnerabilities & exploits
Set up cloud-based infrastructure
Perform vulnerability scans & analysis
Learn remediation best practices

